This affects OpenSSL versions including 1.0.1f which is the version on my up-to-date Mavericks computer Mac (because I used port/brew to install other software which updated my openssl without me realizing it): $ openssl version OpenSSL 1.0.1f 6 Jan 2014 This demonstrates I am not using the Mavericks version of OpenSSL.
Tonight I'm going to discuss OpenSSL for Matlab – which has been tested against Matlab for Windows and Mac OS X.

- $ openssl genpkey -algorith RSA -aes-256-cbc -outform PEM -out yourname.pem -pkeyopt rsakeygenbits:4096 The options: are. Genpkey is the new command for generating keys, it supercedes the old genrsa method. Mac OS X's default OpenSSL does not have this command so building your own version is required.
- VMware Fusion is a software hypervisor developed by VMware for Macintosh computers. VMware Fusion allows Intel-based Macs to run virtual machines with guest operating systems—such as Microsoft Windows, Linux, NetWare, Solaris, or a different version of macOS—within the host macOS operating system.
This code was written strictly to make it easier to look at various algorithms and modes under different circumstances. However, its a neat tool and has many uses beyond its original intentions.
– First step (assuming you already have Matlab) is to build the project. BuildMex is a helper routine to automatically complete the process. If you change the default install path of OpenSSL that change will need to be taken into account in buildMex. I think the path and potential change that may be necessary is obvious (ispc() – is windows only):
if(ispc())
options = [‘ C:opensslliblibeay32.lib -IC:opensslinclude ‘ options];
elseif(isunix())
options = [options ‘ -I/usr/local/ssl/lib -lssl -lcrypto ‘];
end
– Step two, now that everything is built we need to make sure everything is working, example.m will verify that.
This is the output:
So, now that we know everything is working lets take a look at whats going on. I'm not going to give an overly in depth description of OpenSSL, but I will describe this tool and the inputs which feed directly into OpenSSL. Look for a more in depth discussion on OpenSSL in the future.
I'm going to start with a simple example and work up from there.
% Test 1a: Basic Encryption / Decryption
dataToEncrypt = uint8(1:255);
encryptedData = mexEVP_Encrypt(‘data',dataToEncrypt);
decrypted = mexEVP_Decrypt(‘data',encryptedData);
This example starts by generating data of type UINT8. It then encrypts it and decrypts it. If you were to plot dataToEncrypt & encryptedData it will look like this:
Mac Update Openssl
While the example above is powerful, it doesn't support doubles – the primary Matlab data type. We need a way to convert from double to uint8 and back again with out losing data. Which leads to example 2:
%Test 2: Data Conversion
dataStart = 1:255;
toUint8 = [];
for J=1:length(dataStart)
temp = double2uint8(dataStart(J));
toUint8 = [toUint8; temp];
end
toDouble = [];
for J=1:8:length(toUint8)
temp = uint82double(toUint8(J:J+7));
toDouble = [toDouble; temp];
end
The code above is straight forward with a basic understanding of whats happening. Keep in mind a double is 8 bytes and a uint8 is 1 byte and there are 8 bits in 1 byte. So each double in the dataStart array needs to be converted to a uint8 – the first loop accomplishes that. It iterates over each element and appends it to the toUint8 array – which will have 8x more elements than the input array. The toUint8 array could be passed in the mexEVP_Encrypt function at this point as in the first example. The avid Matlab user will also notice the guts of each loop can be reduced to 1 line – more on that in a few minutes.
So lets assume we have just returned from the mexEVP_Decrypt function – we will need to convert the uint8 array back to doubles. This loop looks pretty similar to the first loop with one major difference – the number of elements being passed into uint82double. Since the are 8 bytes in a double – 8 bytes need to be passed in. Thats why J:J+7 is passed in – 8 bytes are passed in and 1 double (8 bytes) is returned.
With any luck you know have a basic understanding of how to encrypt and decrypt data that is a uint8 or a double. We are missing a few key things at this point like:
- Which algorithm – with mode and size is being run?
- What key is being used to encrypt my data?
- What IV is being used in tandem to encrypt my data?
I'm going to point out the included help – if you run mexEVP_Encrypt with no inputs this will output:
mexEVP_Encrypt:
data: What data would you like to encrypt? This is the only required option…
key: what key would you like the data it be encrypted with?
Openssl Mac Os Sierra
IV: The initialization vector used to speed some algorithms up
Supported Ciphers: (Reference OpenSSL documentation for current & complete list)
Currently Defaults to: aes-128-cbc
AES: aes-128-ecb, aes-128-cbc, aes-192-ecb, aes-192-cbc, aes-256-ecb, aes-256-cbc
Blowfish: bf-ecb, bf-cbc, bf-cfb, bf-ofb
Cast: cast-ecb, cast-cbc, cast-cfb, cast-ofb
DES: des-ecb, des-cbc, des-cfb, des-ofb
DESX: desx
3DES: des-ede3, des-ede3-cbc, des-ede3-cfb, des-ede3-ofb, des-ede, des-ede-cbc, des-ede-cfb, des-ede-ofb
IDEA: idea-ecb, idea-cbc, idea-cfb, idea-ofb
I'm also going to point out one other functions: mexRandom
mexRandom can be used to generate a random Key & IV though the official OpenSSL mechanism.
Lets put the basic understanding together with everything else we learned so far – into one large example:
% Test (not in example.m): Encryption / Decryption – random key, iv & custom algorithm
dataToEncrypt = 1:0.25:25;
[key, iv] = mexRandom(‘key','iv');
toUint8 = [];
for J=1:length(dataToEncrypt)
toUint8 = [toUint8; double2uint8(dataToEncrypt(J))];
end
encryptedData = mexEVP_Encrypt(‘data',toUint8,'key',key,'iv',iv,'cipher','bf-cbc');
decrypted = mexEVP_Decrypt(‘data',encryptedData,'key',key,'iv',iv,'cipher','bf-cbc');
toDouble = [];
for J=1:8:length(decrypted)
toDouble = [toDouble; uint82double(decrypted(J:J+7))];
end
Which can be easily verified by summing the difference of dataToEncrypt and toDouble:
Openssl Mac Os X Download
>> sum(dataToEncrypt – toDouble')
- $ openssl genpkey -algorith RSA -aes-256-cbc -outform PEM -out yourname.pem -pkeyopt rsakeygenbits:4096 The options: are. Genpkey is the new command for generating keys, it supercedes the old genrsa method. Mac OS X's default OpenSSL does not have this command so building your own version is required.
- VMware Fusion is a software hypervisor developed by VMware for Macintosh computers. VMware Fusion allows Intel-based Macs to run virtual machines with guest operating systems—such as Microsoft Windows, Linux, NetWare, Solaris, or a different version of macOS—within the host macOS operating system.
This code was written strictly to make it easier to look at various algorithms and modes under different circumstances. However, its a neat tool and has many uses beyond its original intentions.
– First step (assuming you already have Matlab) is to build the project. BuildMex is a helper routine to automatically complete the process. If you change the default install path of OpenSSL that change will need to be taken into account in buildMex. I think the path and potential change that may be necessary is obvious (ispc() – is windows only):
if(ispc())
options = [‘ C:opensslliblibeay32.lib -IC:opensslinclude ‘ options];
elseif(isunix())
options = [options ‘ -I/usr/local/ssl/lib -lssl -lcrypto ‘];
end
– Step two, now that everything is built we need to make sure everything is working, example.m will verify that.
This is the output:
So, now that we know everything is working lets take a look at whats going on. I'm not going to give an overly in depth description of OpenSSL, but I will describe this tool and the inputs which feed directly into OpenSSL. Look for a more in depth discussion on OpenSSL in the future.
I'm going to start with a simple example and work up from there.
% Test 1a: Basic Encryption / Decryption
dataToEncrypt = uint8(1:255);
encryptedData = mexEVP_Encrypt(‘data',dataToEncrypt);
decrypted = mexEVP_Decrypt(‘data',encryptedData);
This example starts by generating data of type UINT8. It then encrypts it and decrypts it. If you were to plot dataToEncrypt & encryptedData it will look like this:
Mac Update Openssl
While the example above is powerful, it doesn't support doubles – the primary Matlab data type. We need a way to convert from double to uint8 and back again with out losing data. Which leads to example 2:
%Test 2: Data Conversion
dataStart = 1:255;
toUint8 = [];
for J=1:length(dataStart)
temp = double2uint8(dataStart(J));
toUint8 = [toUint8; temp];
end
toDouble = [];
for J=1:8:length(toUint8)
temp = uint82double(toUint8(J:J+7));
toDouble = [toDouble; temp];
end
The code above is straight forward with a basic understanding of whats happening. Keep in mind a double is 8 bytes and a uint8 is 1 byte and there are 8 bits in 1 byte. So each double in the dataStart array needs to be converted to a uint8 – the first loop accomplishes that. It iterates over each element and appends it to the toUint8 array – which will have 8x more elements than the input array. The toUint8 array could be passed in the mexEVP_Encrypt function at this point as in the first example. The avid Matlab user will also notice the guts of each loop can be reduced to 1 line – more on that in a few minutes.
So lets assume we have just returned from the mexEVP_Decrypt function – we will need to convert the uint8 array back to doubles. This loop looks pretty similar to the first loop with one major difference – the number of elements being passed into uint82double. Since the are 8 bytes in a double – 8 bytes need to be passed in. Thats why J:J+7 is passed in – 8 bytes are passed in and 1 double (8 bytes) is returned.
With any luck you know have a basic understanding of how to encrypt and decrypt data that is a uint8 or a double. We are missing a few key things at this point like:
- Which algorithm – with mode and size is being run?
- What key is being used to encrypt my data?
- What IV is being used in tandem to encrypt my data?
I'm going to point out the included help – if you run mexEVP_Encrypt with no inputs this will output:
mexEVP_Encrypt:
data: What data would you like to encrypt? This is the only required option…
key: what key would you like the data it be encrypted with?
Openssl Mac Os Sierra
IV: The initialization vector used to speed some algorithms up
Supported Ciphers: (Reference OpenSSL documentation for current & complete list)
Currently Defaults to: aes-128-cbc
AES: aes-128-ecb, aes-128-cbc, aes-192-ecb, aes-192-cbc, aes-256-ecb, aes-256-cbc
Blowfish: bf-ecb, bf-cbc, bf-cfb, bf-ofb
Cast: cast-ecb, cast-cbc, cast-cfb, cast-ofb
DES: des-ecb, des-cbc, des-cfb, des-ofb
DESX: desx
3DES: des-ede3, des-ede3-cbc, des-ede3-cfb, des-ede3-ofb, des-ede, des-ede-cbc, des-ede-cfb, des-ede-ofb
IDEA: idea-ecb, idea-cbc, idea-cfb, idea-ofb
I'm also going to point out one other functions: mexRandom
mexRandom can be used to generate a random Key & IV though the official OpenSSL mechanism.
Lets put the basic understanding together with everything else we learned so far – into one large example:
% Test (not in example.m): Encryption / Decryption – random key, iv & custom algorithm
dataToEncrypt = 1:0.25:25;
[key, iv] = mexRandom(‘key','iv');
toUint8 = [];
for J=1:length(dataToEncrypt)
toUint8 = [toUint8; double2uint8(dataToEncrypt(J))];
end
encryptedData = mexEVP_Encrypt(‘data',toUint8,'key',key,'iv',iv,'cipher','bf-cbc');
decrypted = mexEVP_Decrypt(‘data',encryptedData,'key',key,'iv',iv,'cipher','bf-cbc');
toDouble = [];
for J=1:8:length(decrypted)
toDouble = [toDouble; uint82double(decrypted(J:J+7))];
end
Which can be easily verified by summing the difference of dataToEncrypt and toDouble:
Openssl Mac Os X Download
>> sum(dataToEncrypt – toDouble')
ans =
0
Now I that that we now the output is valid look at the inputs.
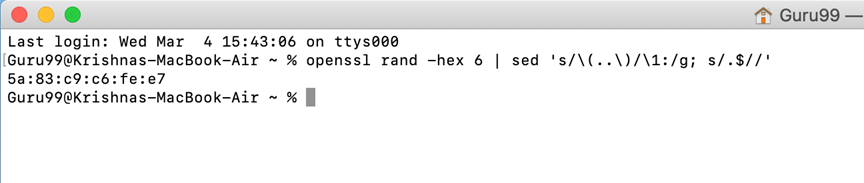
mexRandom is generating a key and and an iv, here is a sample key:
